Self-Hosted Enterprise Search
Ask questions and get answers from your internal knowledge with document-level permissions, on your private cloud of choice.





Only Atolio Protects Your Data the Way You Do.

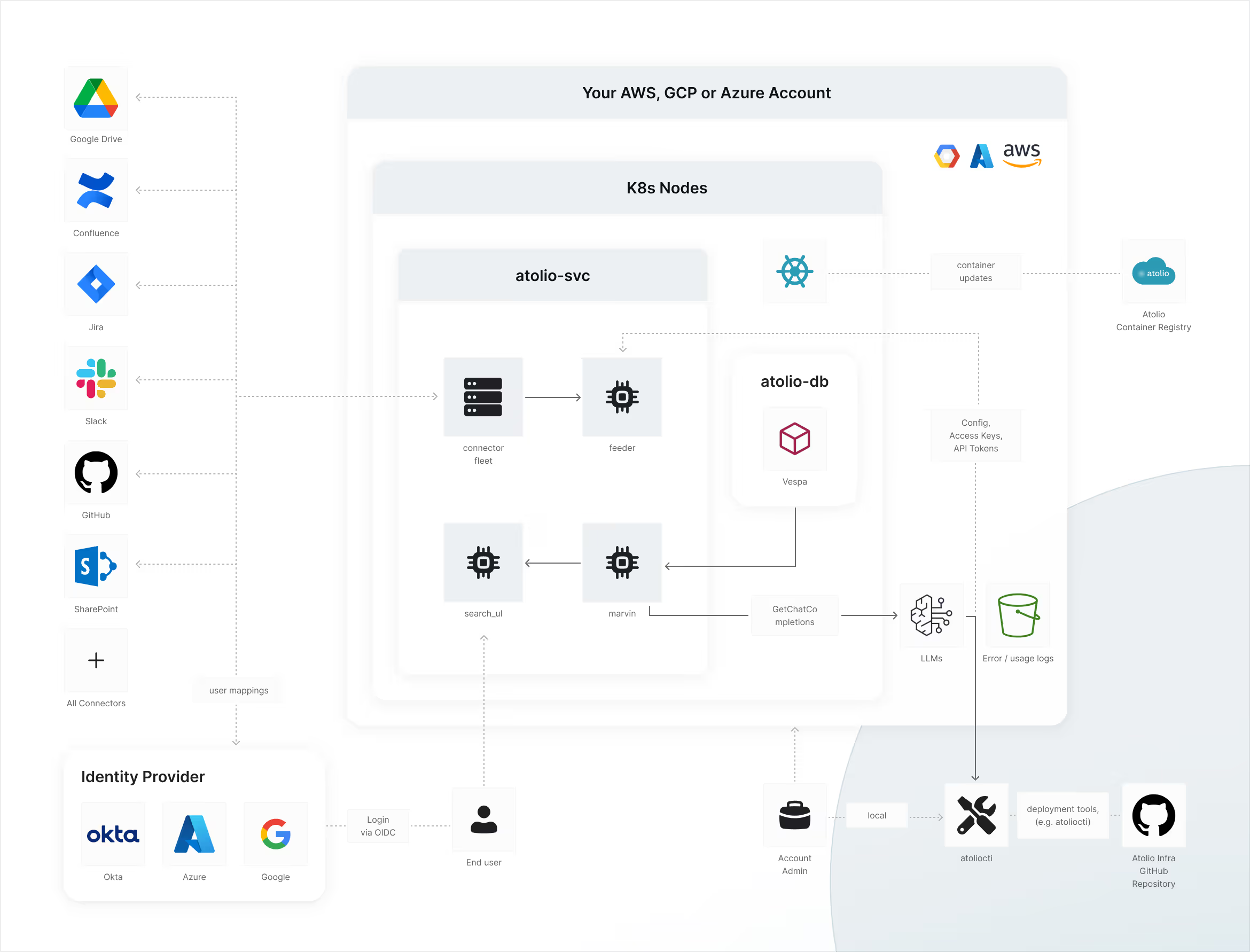
Your Data, Your Cloud
The Atolio deployment and all of your data reside entirely within your own AWS, Azure, or GCP environment, solely under your control.
LLMs Deployed Locally or Via Your Cloud Provider
We are built to leverage your language models of choice, deployed wherever makes sense for your business.

Integrations with Identity Providers
Atolio provides granular document, object, and system-level permissions, ensuring precise access control. Manage who sees what, safeguarding sensitive data while supporting secure collaboration.

Architecture Diagram
Discover the impact when teams can self-serve the
knowledge they need, right when they need it.
Security & Compliance FAQs
What is Atolio's approach to security, compliance, and privacy?
Atolio's security model is built on three principles: private infrastructure deployment, zero data egress to Atolio's systems, and strict adherence to the permission controls of every connected source. Every Atolio deployment runs within your organization's private cloud environment (AWS, GCP, or Azure). No indexed content or query data leaves your infrastructure boundary to reach Atolio-operated systems. Atolio personnel do not have access to your data during normal operation. This eliminates the third-party data processor risk inherent in SaaS platforms that ingest customer content into shared infrastructure.
Permission enforcement is applied at the index layer. Every document retains the access control metadata from its source system. At query time, results are filtered to only surface content the querying user is authorized to see, evaluated for every query, not as a one-time snapshot. Group memberships and role hierarchies are resolved from your identity provider and applied accurately.
On compliance, Atolio's architecture was designed to align with enterprise security requirements including GDPR data residency obligations, HIPAA workload requirements, and more. Because your data remains 100% within your security perimeter when using Atolio, we support compliance requirements you are subject to versus introducing new points of exposure, as traditional SaaS platforms do. Atolio supports SSO identity provisioning and integrates with Okta, Microsoft Entra ID, Keycloak, and Google Workspace.
Data at rest is encrypted using your cloud provider’s best practices, typically AES256. Data in transit uses TLS 1.2 or higher. Encryption keys are managed within your environment using your organization's KMS. Atolio does not hold your keys.
Is Atolio self-contained? How do data flows work?
Yes. Atolio operates as a self-contained system within your private cloud infrastructure, with no data flowing to Atolio's systems during normal operation. Atolio does not send queries, retrieved documents, or user activity to Atolio-operated infrastructure at any point. Connectors pull content from your authorized source systems and write it to an index that lives entirely within your environment. All search queries, result generation, and AI feature execution happen within that same boundary.
The only network calls that occur are those you explicitly configure: calls to your model provider API (Azure OpenAI, Anthropic, Google Vertex AI, or others) and to/from your configured data sources. These calls originate from your infrastructure using credentials you control. These calls do not route through Atolio's systems.
Atolio personnel do not access your environment unless you explicitly grant temporary, scoped access for implementation or support. All such access is logged and auditable.
Because Atolio does not process your indexed content in Atolio-operated infrastructure, Atolio does not function as a data processor under GDPR for that content. This simplifies your data processing agreement obligations compared to SaaS deployments with shared data infrastructure.
How does Atolio prevent hallucinations and ensure answer accuracy?
Atolio limits hallucinations through strict retrieval-augmented generation: every AI-generated response is built from content retrieved from your Atolio index, and every claim is traceable to a cited source document. Responses are synthesized from retrieved passages only, and the model is constrained to those inputs. This addresses the primary hallucination mechanism, where a model generates plausible-sounding content without grounding it in verified source material.
Source citations are surfaced alongside every generated answer so users can inspect the originating document, author, and system of record. If retrieved content does not contain sufficient information to answer a query, Atolio signals low-confidence or no-answer, rather than generating a speculative response.
Because Atolio only indexes content your organization has explicitly connected, the knowledge boundary is defined and controlled. Answer accuracy is directly tied to the quality and currency of your connected content, not to a generalized model knowledge base.
Does Atolio provide audit logging? How does Atolio handle insider threats or malicious queries?
Atolio maintains comprehensive audit logs of all user activity: search queries, document retrievals, admin configuration changes, and connector access events, written to your environment and accessible to your security team. Audit log fields include user identity, timestamp, query content, retrieved document identifiers, and action type. Logs are structured for SIEM integration and support retention policies aligned to your compliance requirements.
For insider threat scenarios, Atolio's permission model is the primary defense: users cannot retrieve content beyond their existing source-system permissions, regardless of how they phrase a query. Search does not function as an access escalation mechanism.
Audit logs enable post-hoc investigation of anomalous access patterns. Because every retrieval event is logged with user identity and document identifiers, security teams can reconstruct what a specific user accessed and when. SIEM or UEBA integration enables real-time alerting on unusual query behavior.
Does Atolio perform application security testing (SAST/DAST)?
Yes. Atolio performs both static application security testing (SAST) and dynamic application security testing (DAST) as standard parts of its software development lifecycle. SAST is integrated into the CI/CD pipeline and runs automatically on every code change to identify insecure patterns, vulnerable dependencies, and misconfiguration before deployment. DAST is conducted against running instances to test application behavior under adversarial inputs, including injection attacks, authentication bypass, and session handling vulnerabilities.
External penetration testing is conducted on a defined cadence by a third-party security firm. Results drive remediation prioritization and inform the ongoing security roadmap.
Atolio provides a vendor security package that includes architecture documentation, network diagrams, and penetration test summary (available to enterprise customers under NDA), as part of the security review process.
How does Atolio handle encryption key management?
Atolio supports bring-your-own-key (BYOK) encryption, giving your organization full control over the keys used to protect data at rest in your Atolio deployment. Data at rest is encrypted with AES-256. Keys are managed in your private cloud using your organization's key management service: AWS KMS, Google Cloud KMS, or Azure Key Vault. Atolio does not hold or access your encryption keys.
Data in transit is encrypted using TLS 1.2 or higher for all connections between Atolio components and between Atolio and connected source systems.
Key rotation is managed by your organization according to your own policies and compliance requirements. Atolio's architecture supports key rotation without requiring re-indexing or service interruption.
What is Atolio's data retention policy?
Atolio's data retention is controlled by your organization, because Atolio is deployed within your private infrastructure, all indexed content and metadata is retained in your environment under your own policies. Atolio does not impose a default retention period. Retention is governed by your data governance policies and the lifecycle of connected source systems. When a document is deleted or access-revoked in a source system, Atolio's connector removes or suppresses that content from the index during the next delta sync cycle.
Content can also be excluded proactively. Administrators configure source-level filters or content exclusion rules that prevent specific content types, containers, or labeled documents from being ingested.
When a contract ends, Atolio does not retain copies of your data in Atolio-operated infrastructure. Offboarding includes a documented data deletion process to confirm all indexed content is purged.
Get the answers you need from your enterprise. Safely.
Experience how AI-powered enterprise search can transform your organization's knowledge management and unlock enterprise insights.
